
ELBRUS
Security and Access
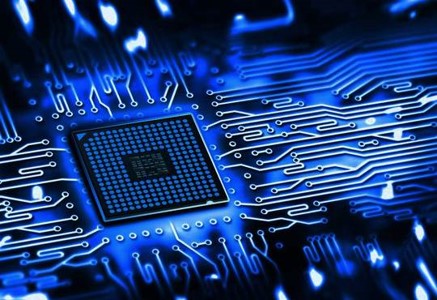
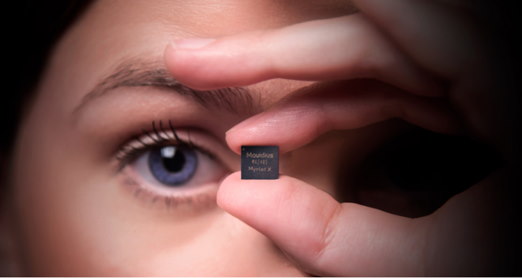
Silicon at the speed of software
Design Arm amd RISC Cpu in very short time
introduce ELBRUS Security and Access
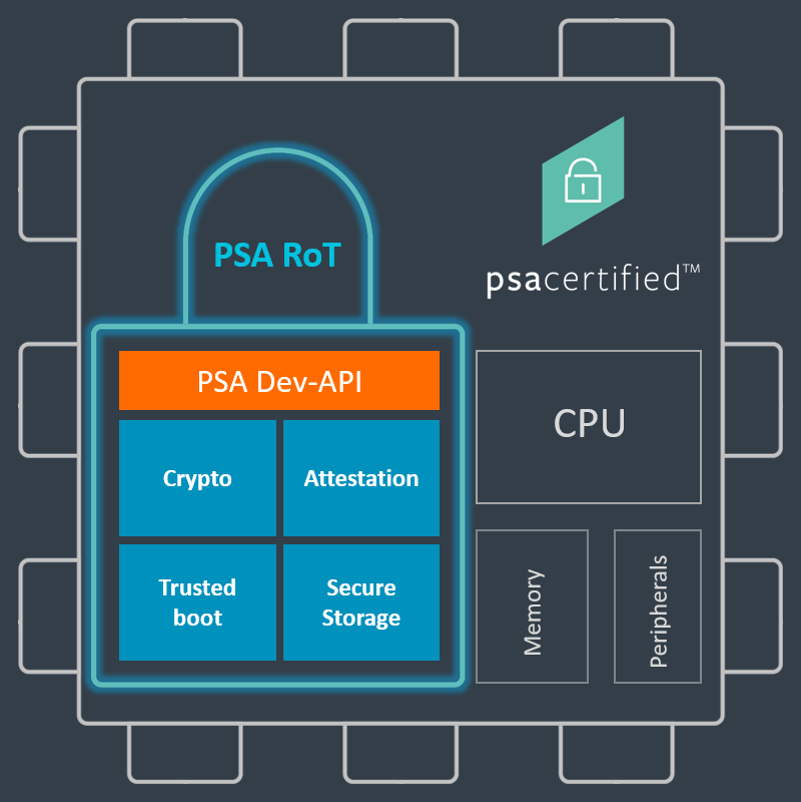
Trust Zone
Trust Zone is an extension to the development toolchain Elbrus Security Framework and enables application developers to deliver secure, encrypted code. We already implemented all layer of security by The development team is able to easily import the organization’s security configuration profile without potentially compromising it. Since the correct security and encryption settings are automatically included, the developers can focus on the functionality of the application. After building and debugging the application code as usual with Elbrus Security Framework, the code will be automatically mastered and encrypted using Advanced Encryption Standard (AES). Once programmed into the MCU, the application can be updated with secure code verified by the Secure Boot Manager.
Adding security functions to Elbrus Platfrom securityFramework
With Trust Zone, you extend the capabilities of Elbrus Embedded Workbench to enable secure mastering based on a Security Context that is created by an Embedded Trust user, or by using a pre-defined Security Context Profile. By making use of this scaled-down version of the full security environment, you gain two things: Increase security by limiting the number of people able to access and control the application security to a bare minimum. Let the application developers focus on doing their thing: creating beautiful code and differentiating functionality. Using the right tools, you can trust your application and create for the future. Security Context We provide a number of pre-defined Security Context Profiles for you to get started developing secure applications. The Security Context defines the configuration of the trusted execution environment. It is a description of the security environment that is required to protect your application. The properties of the pre-defined Security Context Profile include: Cryptographic keys and certificates Secure Boot configuration Device security Application update process Update policy Device memory layout Note that in order to change a Security Context, or build a new one from scratch, you will need to use Embedded Trust
Adding security functions to Elbrus Platfrom securityFramework
we provide a number of pre-defined Security Context Profiles for Government to get started developing secure applications for Fiscalization and Distribution Switch and secure payment in different level. The new technology implemented theorically S2M inside main chip to avoid huge of transaction in low security. The power of CPU and parallel processing all Switch transaction process handle in this side. Also this is very good for high security Ledger The Security Context defines the configuration of the trusted execution environment. It is a description of the security environment that is required to protect your application. We are focusing on Government and large organization to prepare complete security solution in different level The properties of the pre- defined Security Context Profile include:
- Cryptographic keys and certificates
- Secure Boot configuration
- Device security
- Application update process
- Update policy
- Device memory layout
- E-Payment total solution
E-Government
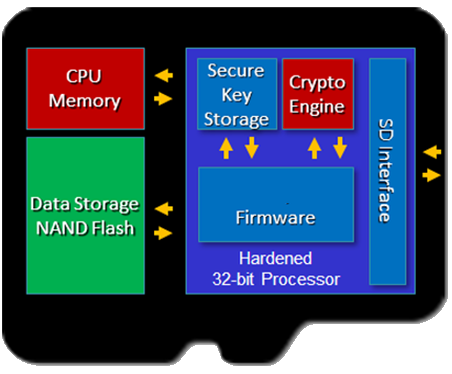
EL10XPS
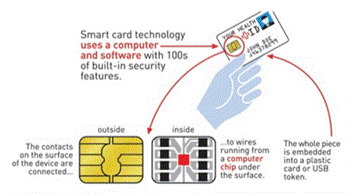
EL10XPS is a 64-bit high performance and large capacity Encryption IC.It integrates multiple special security algorithms and provides a lot of external interfaces to connect any device as Peripheral . It is suitable for using in financial payment cards, Fiscal industrial application cards, identification, security storage and so on.
Typical application

Financial Operator Keys

Mobile payment

Block chain wallet

eToken

E-Finanace
ELB1244S
Using a 64 bit processor, the ELB1244S IC supports ISO/IEC 14443 contactless protocol (Type A/B) and multiple GPIO interfaces. It has some features of low power consumption, high stability to work different and strong compatibility.
Typical application
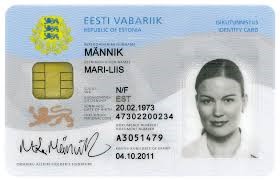
ID card
Bank card

NFC Card

NFC Card
Driving License
E-health

E-Commerce
EL10XPS
Nowadays all Ecommerce and software token under very high attack. So identification and authentication are important matter to any transaction. ELB10OP uses a security micro-controller based on zEnergy Very-lowest power consumption technology which is independently developed by Elbrus Technology. It features almost zero power consumption, high integration and fewer off-board components. With built-in RTC circuit, LCD drive circuit and a power supply management circuit, and it was integrated several algorithm for hardware security.


AI AND IOT
Our technologies on Camera make a revolution in Camera industries. enabling features like person detection, object classification, analytics, and more—performing complex data analysis in real time, delivering breathtaking imagery, and preserving vital system resources such as power and network bandwidth. We specialize in the development of iOT camera, scalable designs for intelligent cameras, offering a proven path to mass production. two Model SOC to make camera a range for 8K for high end and low-end. Our chip architecture is based on a deep understanding of computer vision algorithms based on FPGA or SOC on Risc and Arm processor. Its not like other general-purpose CPUs and GPUs, Our solution includes a dedicated vision processing engine programmed with a high-level algorithm description, allowing our architecture to scale performance to trillions of operations per second with extremely low power consumption.
Typical application

360 DOF Camera

Bullet Camera

Drone Camera
Camera SOC Customization
Camera Acceleration

